The pentesters & the maintenance operators: a mobility paradox
Air‑gapping has long been treated like the Frankfurt Kitchen of cybersecurity. Margarete Schütte-Lihotzky’s design revolutionized domestic architecture in the 1920s by separating the small, functional kitchen from the living spaces. It simplified daily life and improved safety (e.g., managing gas, heat, and tools). But later generations criticized its rigidity as it isolated the person in the kitchen and made misuse common (pre‑defined drawers that didn’t fit real users’ habits). Air‑gapping shares the same story. It was essential, effective, and transformative, but as practices evolved, its limitations appeared: it isolates field teams, complicates collaboration, and introduces operational friction for operational teams, from pentesters to maintenance teams.
When Security Walls Become Operational Barriers
Air-gapping brings out the same paradox as the Frankfurt kitchen did: the conflict between the need to isolate the environment – a cooking environment separated from the sleeping one - and the evolution of operational reality.
In most organizations, users’ workstations are where the business is cooked. Yet, while cybersecurity requires strict uncompromising isolation, modern work has become inherently mobile and fluid. People switch contexts constantly, collaborate with external partners, manage internal tools, and access sensitive resources often from a single device and from multiple locations. And for many roles, this contradiction has become a daily operational burden.
Cybersecurity teams are no exception. Take the case of penetration testers: many travel across the country with several laptops dedicated to distinct client environments. A pentester staying in a hotel may have to open multiple machines at once — one per project — switching between them continuously just to maintain proper separation. Security is preserved, but at the price of ergonomics, productivity, and sanity.
Leftovers: The Cost of Rigid Security for Field Teams
Operational and maintenance teams face another challenge. They usually work in locations where network quality is unreliable. They need to access heavy documentation, sensitive configurations, or industrial dashboards — but cannot depend on 4G, Wi‑Fi, or remote desktops. The result? Either they work blind… or they use poorly secured or outdated devices they can carry and can operate offline, creating additional risks for the organization.
Air-gapping was never made for field teams. And VDI is simply incompatible with their constraints. As for IT and security administrators, this proliferation of physical machines creates a blind spot. Each additional laptop means another OS to maintain, another update cycle to track, another endpoint to monitor. Visibility decreases as the number of devices increases.
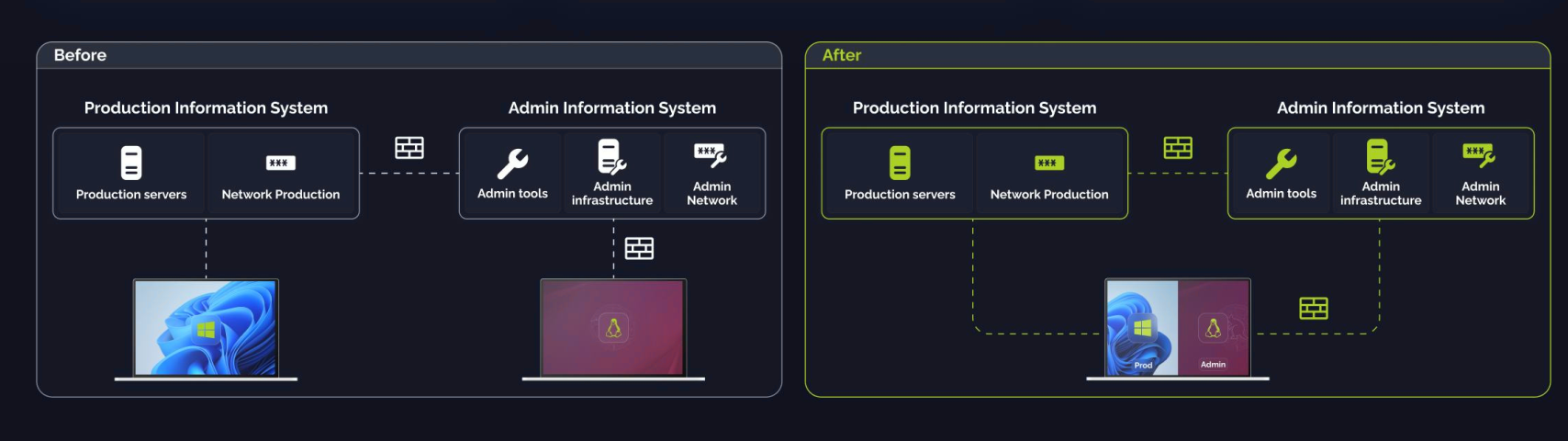
Multi-environment workstations bring the opportunity to finally provide a solution to those users long overlooked by traditional security models. They keep environments strictly separated but consolidate them on a single, secure workstation. Isolation remains uncompromised, but mobility, ergonomics, and IT visibility finally align with modern work realities, including the most sensitive environments.
A technical shift at the service of operational reality
A multi-environment workstation (MEW) bridges the gap between flexibility, security, and performance by embedding isolation directly into the endpoint. No more relying on networks or data centers to compensate for weak devices. With MEWs, the workstation itself becomes the trust boundary. No more lugging multiple machines, no more juggling tokens across sessions, and no more waiting for a stable connection just to start work. Transitioning from a productivity environment to an administrative one no longer requires switching devices—or even moving to another building. The impact is immediate: less cognitive load, fewer authentication headaches, and far fewer error-prone manual steps. By eliminating these frictions, MEWs let teams focus on what truly matters—getting the job done efficiently and securely.
Hardware security: efficiency starts from the kitchen’s design
Organizations’ cybersecurity strategies have long been focused on software. The physical layer has been largely ignored. Multi-environments workstations invite them to change their mindset.
This shift works only when isolation is anchored in hardware rather than left to software convention. A type‑1 hypervisor provides the foundation, but confidence comes from a measured‑boot chain, a hardware root of trust, and a deliberately minimal Trusted Computing Base (TCB) - which covers all hardware and software protections
covers all hardware and software protections. When each environment has its own trust and connectivity assumptions — including dedicated VPNs and tightly controlled local communication paths — administrators stop treating the laptop as a thin terminal and start treating it as a verifiable platform.. When each environment has its own trust and connectivity assumptions — including dedicated VPNs and tightly controlled local communication paths — administrators stop treating the laptop as a thin terminal and start treating it as a verifiable platform.
The result is not “a PC running virtual machines,” but a workstation whose integrity can be attested, whose attack surface is deliberately constrained, and whose failures are far less likely to cascade across domains. It is an opportunity to finally give hardware security the strategic role it deserves.
The benefits for operational teams: usability, efficiency, and security
The operational benefits are immediate, especially for users working with one or multiple Restricted Distribution environments. Multi-environment workstations (MEWs) transform daily workflows.
Developers gain the autonomy they need to innovate, while system administrators maintain the visibility and control required to ensure compliance and security. No more trade-offs between flexibility and oversight.
MEWs provide OT operators and industrial or maintenance teams with a single, unified device that hosts both dedicated operational environments—such as SCADA systems or industrial dashboards—and corporate applications. This eliminates the need to juggle multiple machines, nor to hoping for a stable network link before any meaningful work can begin. Multi-environment workstations reduce both physical clutter and the risk of cross-contamination between sensitive systems.
Just as modern kitchens preserve dedicated spaces for cooking while adapting to the way people actually live and work, multi-environment workstations maintain strict isolation without compromising usability or mobility. Finally, a solution that works with your team, enabling them to operate securely and efficiently—without the friction.
Finance and governance: speaking the executive language
For years, cybersecurity investments have been hard to translate into economic value. A recent study reported that 41% of CISOs struggle to express cybersecurity in business terms — making every project appear as a cost rather than a productivity driver.
Financial clarity: fewer devices, lower TCO, measurable ROI
Multi-environment workstations (MEWs) redefine cost efficiency by consolidating multiple isolated environments onto a single device. This shift eliminates the traditional model of workstation proliferation: a cycle of escalating costs driven by more operating systems to maintain, more updates to track, and more endpoints to monitor.
MEWs simplify IT architecture by reducing complexity and providing clearer visibility to sysadmins across the entire infrastructure. No more sprawling device fleets; instead, a streamlined, centralized approach that cuts through the noise of fragmented management. For CISOs and IT directors, MEWs deliver isolation by design, ensuring no communication between environments. This drastically reduces the risk of cross-contamination, aligns with compliance requirements, and minimizes exposure to breaches. The result? A leaner, more secure infrastructure that doesn’t just mitigate risks but actively enhances operational resilience.
The financial impact is immediate and measurable. Organizations slash hardware purchases, reduce maintenance efforts, and cut down on support tickets, logistics, and repetitive setups. These aren’t hypothetical savings—they’re structural gains that free IT and security teams to focus on higher-value work. Fewer devices mean less friction, more productivity, and a sharper focus on what truly matters.
This isn’t about avoiding potential future losses—it’s about generating long-term savings and unlocking valuable time for IT and security teams. A lighter device fleet also improves monitoring for security teams and simplifies asset tracking for finance, making MEWs a strategic investment in both efficiency and peace of mind.
Governance: isolation equivalent to dedicated hardware — recognized by ANSSI
The critical governance question remains: Does multi-environment isolation deliver the same security guarantees as physical separation while meeting stringent data privacy frameworks? For compliant multi-environment workstations, the answer is unequivocally yes, but only when built on a foundation of rigorous design principles.
A compliant multi‑environment workstation answers “yes” — if it follows strict design principles:
- each user environment implemented as an independent, isolated VM,
- a hardened base system with secure boot, TPM, and full‑disk + memory encryption,
- strict isolation of CPU, memory, storage, I/O, and networks,
- trusted display paths, strong authentication, and controlled updates,
- no inter‑domain communication except through tightly governed one-way mechanisms,
- lifecycle‑long documentation, hardening, and attestation.
These principles align seamlessly with ANSSI’s segmentation and endpoint isolation guidelines, providing a framework that satisfies even the most demanding regulatory requirements. Where traditional network segmentation has long been the standard for securing critical systems—albeit at significant financial and operational cost—multi-environment workstations shift the paradigm to the endpoint itself. This approach enables precise, surgical isolation of domains without the complexity or inefficiency of physical separation.
The result is a lighter, more agile operational model: fewer devices to certify, simplified compliance processes, and restored visibility and control. Physical separation alone is no longer sufficient in today’s dynamic threat landscape. By embedding isolation at the endpoint level, organizations regain governance without the burden of device sprawl—redefining security not as a constraint, but as a strategic enabler.
Physical separation alone is no longer enough. Endpoint-level isolation brings back control, visibility, and governance without multiplying devices.
Conclusion: toward a new paradigm
Multi-environment workstations mark a turning point in sensitive environment isolation. Modern work practices have exposed the first cracks in air-gapping’s dominance. This model doesn’t just fail to adapt but actively ignores user experience. At KERYS, we’ve long understood that when user experience is overlooked, security becomes fragile. People will always take the easiest path to get their work done, even if it’s not the safest or most visible to administrators.
Embedding guardrails directly into the workstation reduces the incentive to bypass them and restores alignment between usability and protection. Since day one, we’ve been building the only type-1 hypervisor that fully isolates sensitive environments without compromising security or user experience. Long before ANSSI’s guidelines, we provided a compliant alternative to physical separation, helping organizations simplify their IT infrastructure without compromise of security or user experience. Does it sound too good to be true? Let us show you a way out of air gapping.